Lesson 4: Routers and Redundancy
Widget
Overview
Students spend most of today’s lesson in an updated Internet Simulator that lets students send messages with a dedicated To and From IP Address. Students start by connecting to a dedicated router and sending messages only to each other. They look at the router logs to find other students on different routers, then send messages to those students. They look at the router logs again to notice that messages are being passed between routers in order to reach their destination. Students continue to send messages and view the logs one last time to notice that the messages are also taking different paths to reach the same destination. The lesson wraps-up by introducing new vocabulary and using these words to summarize today’s activity.
Purpose
After yesterday’s lesson that motivated the need for some kind of addressing system, today’s lesson has students use IP Addresses to send messages to specific people. Today’s focus is on how routers help manage the paths that different messages take. The router logs are an important tool for students to discover the extra work that routers are doing to send messages - they can see that messages are passed between routers and that messages take different paths along the way, all from analyzing the data in the router logs. Importantly, students should make a connection between these observations about multiple pathways and the concept of fault-tolerance - because there are multiple pathways, the internet can continue to function even when there may be an issue that the routers need to address.
Agenda
Lesson Modifications
Warm Up (5 mins)
Activity (35 mins)
Wrap Up (5 mins)
View on Code Studio
Objectives
Students will be able to:
- Explain how data is routed through the Internet
- Describe how the redundant nature of networks can lead to dynamic, fault tolerant routes
Preparation
- Read through Teacher Guide - Routers & Redundancy - Unit 2 Lesson 4 - Activity Guide in order to:
- Test the Internet Simulator to understand how the tool works
- Prepare routers ahead of time so they are available for students to join when the activity starts
- Decide how you will be proactive to avoid students sending inappropriate messages and prepare for how you will react should this happen anyway
Links
Heads Up! Please make a copy of any documents you plan to share with students.
For the Teachers
- CSP Unit 2 - The Internet - Presentation
- Teacher Guide - Routers & Redundancy - Unit 2 Lesson 4 - Activity Guide
Teaching Guide
Lesson Modifications
 Attention, teachers! If you are teaching virtually or in a socially-distanced classroom, please read the full lesson plan below, then click here to access the modifications.
Attention, teachers! If you are teaching virtually or in a socially-distanced classroom, please read the full lesson plan below, then click here to access the modifications.
Warm Up (5 mins)
Discussion Goal
Goal: Students will probably identify that both systems involve a numerical address that helps identify where the letter should go, and that both a 'to' and 'from' address are needed.
However, something that may be less obvious is that our postal system has several intermediary steps before it reaches the destination - it is picked up by a postal worker, sorted in a postal center, and eventually directed to the recipient. This point is helpful in foreshadowing how today's lesson builds on yesterday's activity and the introduction of routers.
Prompt: At the end of class yesterday, we saw that the Internet uses the Internet Protocol and IP Addresses to communicate across the shared Internet. How is this system similar to how we send letters in the mail? How is it different?
Teaching Tip
Before starting this lesson, it is helpful to test the widget that students will be using and to have some additional routers setup ahead of time. These steps are in a separate document - Teacher Guide - Routers & Redundancy - Unit 2 Lesson 4 - Activity Guide
Remarks
Today we will investigate how the Internet Protocol helps us communicate on the internet, and we will use new devices called routers to help manage how we communicate.
Activity (35 mins)
Group: Place students into groups of 3-4. Assign each group a number.
Teaching Tip
Responsible Messaging: This simulator can feel like an anonymous chat program and students may send overly personal or non-school appropriate messages to each other. Here are some strategies to avoid this:
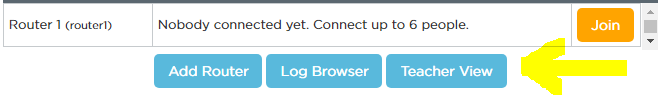
- Be Proactive & Upfront: let students know their messages are being monitored and can be traced back to their accounts. There is a ‘Teacher View’ button you can use to see the username of who sent individual messages (see below)
- Avoid Downtime: Unstructured time in the lesson can lead to off-task messages. As best as you can, try to keep the pace of the lesson moving so there is always something for students to do
- Provide Specific Prompts: This lesson includes several specific types of messages for students to send. There is never a point where students are asked to send ‘whatever you want’ to another student in the class.
Remarks
Today we are using a new version of the Internet Simulator that incorporates the IP addresses we learned about yesterday. In fact, when you log onto the Internet Simulator today, you will notice that now everyone has their own IP Address, which will be important in today’s simulation.
Do This:
-
Log into Code Studio and connect to the same router as your group number.
-
Use this new version of the Internet Simulator to say hello to each person connected to your same router.
Circulate: Ensure that everyone in the class understands how the widget works before continuing. Guide students to see how to use the IP Addresses to communicate. If students in the group figure it out quickly, encourage them to share with other group members.
Remarks
In yesterday’s lesson, everyone was directly connected to everyone else and we could see all of the messages. In today’s lesson, we’re connected to a router which helps decide which messages we receive. We can even take a look inside the router to see the decisions it is making
Teaching Tip
Viewing the Logs: In order to follow along with the class, you may need to join a router yourself and click into the log browser with the students. You can also access the log browser from the "Connect to a Router" screen - there is a Log Browser button right next to the Add Router button.
Why So Many Messages? The true goal behind this part of the activity is to generate lots of internet traffic so students will be able to analyze the router logs. Behind the scenes, these routers are bouncing messages amongst themselves and along different paths - all of which will become apparent when we re-examine the router logs in the next part of the activity.
Do This:
-
Have students open the router logs and view the messages being sent on their router.
-
After students have seen their own messages, use the drop-down menu to view the messages across all routers. Students will see all messages sent across all routers and the IP addresses of students on other routers.
-
Use the router logs to choose an IP address from each of the other routers. Send each of those people a message to ask them who they are and one of the following questions:
- What is your favorite food?
- What is your favorite type of animal?
- What is your favorite color?
- Note: Be sure to also respond to questions you get from people on other routers!
Circulate: Monitor students as they send messages. Help students to use the router logs to find other IP Addresses. If students finish, encourage them to continue gathering data from as many people as they can.
Regroup: As a class, open the router logs and view the messages across all router logs. There should now be examples of messages appearing multiple times. Ask students to find one of their own messages and see how many times it appears.
Discussion Goal
Goal: Students should notice that each copy of their message is identical except for the ‘Logged By’ column. This column shows which routers the message is passing through as it travels through the network. This shows that the messages are not taking a direct route to the destination - it may pass through multiple routers before getting to the final destination.
It may be helpful to draw a network diagram on the board (similar to the activity from the second lesson) - even though each user is directly connected to a centralized router (as you can see in the Internet Simulator), the routers are connected to each other and pass messages along the way.
Prompt: Can you predict why some messages are appearing multiple times?
Remarks
Our messages are being sent from router to router, bouncing between different routers in the network. Not all messages take the same path to get to their destination - in fact, even when sending multiple messages to the same person, messages may take different paths.
Discussion Goal
Goal: Students should notice that their messages are taking different paths between routers to get to their destination - one message may take a certain path, while the next message takes a different path. Once this observation is made, the discussion can move to the wrap-up prompt.
Do This:
- Pick someone on a different router and send three separate messages with your top three favorite movies or TV shows.
- After you send the messages, open the router logs and find these same messages in the logs. Notice how these messages traveled through the network. Did they always take the same path from your router to the other router?
- Look at other messages that are being sent. Are there any patterns in the paths that they take?
Prompt: What did you notice about the messages you sent in the router logs? Did they always take the same path from your router to the other router?
Wrap Up (5 mins)
Discussion Goal
Goal: Students may brainstorm several reasons why the messages are taking different paths, such as:
- Some paths have lots of traffic, which can slow down the message. Instead, the router sends the message long a different path.
- One of the paths may have been ‘cut’ like in the activity from Unit 2-Lesson 2, requiring the message to take a different path.
Students should use these new vocabulary words to describe these reasons, especially how the different paths can help make the network fault-tolerant. Students may see these words as having a cause & effect relationship: the redundancy in the network is what helps make it fault-tolerant.
Read: Read the vocabulary on the slide. Students should not put these terms in their journals yet.
Prompt: Thinking about these terms, how can we describe what we've observed in the router logs at the end of this activity? What are some practical reasons that you think messages might take different paths from one router to the other?
Journal: Have students record the vocabulary definitions for the following words: router, redundancy, fault tolerance.
Assessment: Check For Understanding
Check For Understanding Question(s) and solutions can be found in each lesson on Code Studio. These questions can be used for an exit ticket.
Question: Pick Two: If the post office delivered mail exactly like the routers deliver messages on the Internet, which of the following statements would be true?
Question: What are the benefits of building redundancy into a network? What are the potential issues with building redundancy?
- Lesson Overview
- Student Overview
Student Instructions
Student Instructions
In 50 words or less, describe the concept of a number system.
Why are rules required for a number system to be useful?
Standards Alignment
View full course alignment
CSTA K-12 Computer Science Standards (2017)
NI - Networks & the Internet
- 2-NI-04 - Model the role of protocols in transmitting data across networks and the Internet.
- 3A-NI-04 - Evaluate the scalability and reliability of networks, by describing the relationship between routers, switches, servers, topology, and addressing.
- 3B-NI-03 - Describe the issues that impact network functionality (e.g., bandwidth, load, delay, topology).
CSP2021
CSN-1 - Computer systems and networks facilitate how data is transferred
CSN-1.B - Explain how the Internet works.
- CSN-1.B.5 - Routing on the Internet is usually dynamic; it is not specified in advance.
CSN-1.E - For fault-tolerant systems, like the Internet: a. Describe the benefits of fault-tolerance b. Explain how a given system is fault-tolerant c. Identify vulnerabilities in a system.
- CSN-1.E.1 - The Internet has been engineered to be fault-tolerant, with abstractions for routing and transmitting data.
- CSN-1.E.2 - Redundancy is the inclusion of extra components that can be used to mitigate failure of a system if other components fail.
- CSN-1.E.3 - One way to accomplish network redundancy is by having more than one path between any two connected devices.
- CSN-1.E.4 - If a particular device or connection on the Internet fails, subsequent data will be sent via a different route, if possible.
- CSN-1.E.5 - When a system can support failures and still continue to function, it is called fault-tolerant. This is important because elements of complex systems fail at unexpected times, often in groups, and fault tolerance allows users to continue to use the networ
- CSN-1.E.6 - Redundancy within a system often requires additional resources but can provide the benefit of fault tolerance.
- CSN-1.E.7 - The redundancy of routing options between two points increases the reliability of the Internet and helps it scale to more devices and more people.